Technology is progressing at extremely rapid rates. The best solution for companies to take is having a dedicated IT team and providing regular and constant training to employees so they know what to look for.
By Nathan Brainard
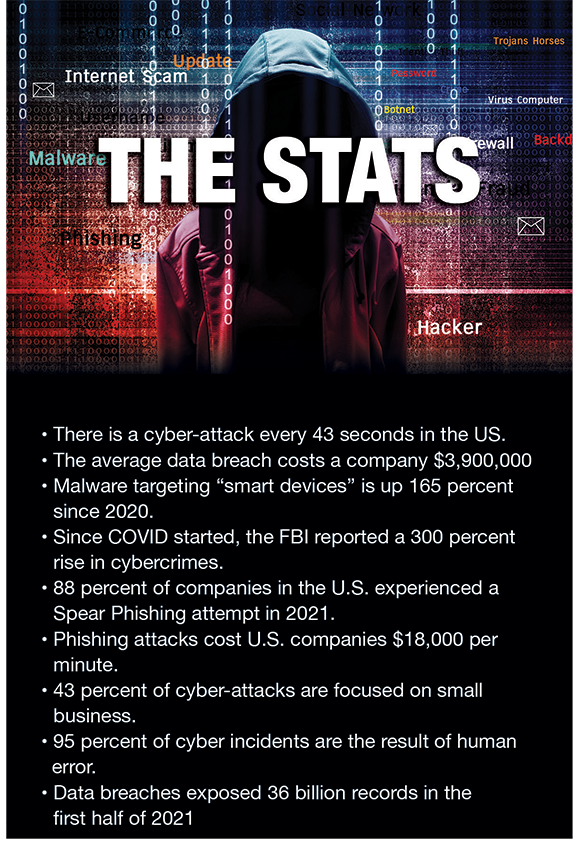
Cyber Liability insurance is typically an afterthought for most companies, but the reality is, the threat is very real and growing by the day. It is not just the Fortune 500 companies who must worry about hackers infiltrating their systems. The threat to private companies is as great, if not greater, than that of the publicly traded sector.
With each passing day, the methods and tactics used by hackers intending to penetrate your network and gain access to your system and records grows. It may not necessarily be that you are considered a marquee target, but rather your system. Even people have shown signs of being easy to access and compromise. Like everything else in life, the path of least resistance often yields the easiest rewards.
COVID brought about a massive shift in not only how we conduct our daily business, but also where we are conducting it. As more of the workforce continues to engage on a daily basis from remote locations such as homes, shared workspaces, or while on vacation, the ability for those who wish to do us harm grows. Our ability to protect our individual devices such as laptops, tablets, and smart phones is paramount, but many companies are not pushing this narrative within their workforce population.

Current Trends
As the situation in the Ukraine continues to develop, we are seeing notices from the U.S. government stating that cyber strikes are not only likely, but also imminent. A great example is the recent barrage of self to self-text messages that were sent in late March to Verizon customers. Service customers received a text message from themselves stating they had made their payment on time and their phone carrier was giving them a small reward. Once clicked upon, they were directed to Channel One Russia, a state TV network. To date, it is not known if other issues arose from clicking on the link, such as permitting access from a third party to your private data, photos etc. So, what has your risk management team done to insulate your company from risk?
To be clear, there is no magic wand solution when it comes to cyber security. The fact remains, a company is only as formidable as their weakest link and in this case, that link is the lowest level employee who never changes their password and is fairly caviler in what links they click, often throwing caution to the wind to see the new most relevant viral video on TikTok, article on Twitter, etc.
Could Your Company Withstand a Breach?
If someone were to ask you if your system could withstand a fortitude of cyber-attacks, can you honestly answer, yes? Do you know if the answer to the question is no? Because technology is ever-evolving, the necessity of constant vigilance is paramount.
If we are being honest, our respective IT departments are overwhelmed. They are onboarding new employees while at the same time disconnecting with those who are no longer with the company. They are trying to make sure employees are not downloading apps that open the system to penetration, are not falling victim to phishing or spear phishing scams, or engaging in risky internet behavior. To say their plates are full is likely an understatement. So, what can companies do to insulate themselves as best as possible?
There is no shortage of companies who specialize in Cyber Security. Many of them offer a suite of services that you can choose from ranging in scope from a basic vulnerability assessment to 24/7 system monitoring. Given each company’s needs are going to be different, any consideration of using an outside firm should be interviewed by a project group that includes, at a minimum, representation from your Risk Management and IT team.
Companies who have data breaches can expect to incur a cost of $650+/- per compromised file related to monitoring, notification, etc. over the course of one year. If you think about the number of files you have in your system, you can easily do the math.
Common Hacking Methods
So, what are the areas hackers look for or methods they use to gain access? Below are some of the most common ways we see perpetrators gain access to a system.
Open Ports
Hackers will do a search to see if a company has any “open ports” in their network. Through a serious of methods and attempts, they try to identify ports that are connected to a network, but have no security surrounding them, such as password protection. Once identified, they can gain access to the system and install malware or seek out specific data they intend to sell or use for ransom.
Malware
Short for malicious software, this is a program designed to spy on users and steal their data. These programs can lay dormant in your system collecting sensitive data and keystrokes until the hacker is ready to pounce. The hacker then takes the stolen information and uses it to take over their target’s system. Malware can also be used to turn on your computer camera and spy on you or turn on your microphone and listen in on conversations.
Social Engineering
This is the art of manipulating, influencing, or deceiving you into taking action that is not in your own best interest or the best interest of your company. The goal is to obtain trust and then exploit that trust to gain access to your network. Hackers have gotten extremely clever in this area. A good example would be you are a new employee, and you receive a phone call from HR that you have missing information from your file, and they would like to rectify it. The caller will then send you an e-mail with a link and will stay on the line to walk you through the issue. Once you clink on the link, they will say that they just found the missing document and they are sorry for disturbing your workday. In some cases, they might be working in tandem with another person and if you start to question the process, they will advise they would like to bring their supervisor on the line, which is done to create a sense of greater security for you to execute what is being asked. Once you have clicked on the link you have given them everything they need to access the system.
Phishing
This is a type of social engineering where an attacker sends a fraudulent message (spoofed, fictitious, etc.) designed to trick a person into revealing sensitive information to the attacker or to deploy malicious software (malware) on the victim’s infrastructure like ransomware. Phishing attacks have become increasingly sophisticated and often mirror the site being targeted allowing the attacker to observe everything while the victim is navigating the site, and transverse any additional security boundaries with the victim. Phishing e-mails will try to install some sense of urgency on the part of the victim to have the victim react/respond before they can really think through what they are being asked to do. If the e-mail you receive states that you have to take immediate action and you were not expecting it, odds are it is an attempt to gain access to your system.
Spear Phishing
This involves an attacker directly targeting a specific organization or person with tailored phishing communications. This is essentially the creation and sending of e-mails to a particular person to make the person think the e-mail is legitimate. In contrast to bulk phishing, spear phishing attackers often gather and use personal information about their target to increase their probability of success of the attack. They will gather the information on their target via social media and other available outlets. Spear phishing typically targets executives or those that work in financial departments who have access to the organization’s sensitive financial data and services.
Ransomware
Ransomware is a type of malware that scrambles files, making them unreadable/inaccessible. Files are then held hostage until payment is made to remove the malware encryption. Payment is often requested in Bitcoin or other forms of Cryptocurrency, as it is easy for the hackers to move around even though it can be tracked. Should you fail to respond to their initial request, the hackers will often increase their demand or threaten to wipeout your data. Refusing to pay the ransom can result in serious damage to your network and records, it can cause substantial operational issues for the company. In addition to the internal damage, this sort of attack can have, it can also kill productivity and the company’s reputation and cause inflated financial expense given the time needed to resolve the matter and restore the system to a time prior to the ransomware infecting the system.
Know What to Look For
Technology is progressing at extremely rapid rates. The types of attacks we are discussing here may be outdated by the time you read this article and a new type of threat could be working its way around the world. The best solution for companies to take is having a dedicated IT team and providing regular and constant training to employees so they know what to look for. This can include classroom or web-based training sessions, simulated phishing and other types of e-mails to see who is opening them and potentially exposing the company etc. The hackers are extremely savvy and will continue to find ways into the companies and systems that they target. Only through extreme vigilance can their attempts be thwarted. | WA
Nathan Brainard, AAI, is a Regional President at Insurance Office of America (IOA) (Longwood, FL) and a member of the NSWMA Safety Committee. Nathan has been with IOA for seven years and specializes in Environmental Insurance with an emphasis on insurance for the Waste, Recycling, Remediation and Demolition industries. He can be reached at (407) 998-5287 or via e-mail at [email protected].